
TCP/IP Model: DHCP and NAT in Network layer
To properly learn something, we have to start at the beginning. We will be learning one concept at a time, process it, and move to the next.
The goal is consistent learning and absorbing information while feeling engaged and not overwhelmed.
I have divided the network layer articles into six parts.
- Introduction to Network layer
- Addressing in Network layer
- Decoupling the Router
- Routing and Routing Protocols in Network Layer
- Internet Protocol
- DHCP and NAT in Network layer
Goal of this article
In this article, I'll focus on key concepts like DHCP and NAT in the network layer.
Dynamic Host Configuration Protocol
Every single computer on a modern TCP/IP-based network needs to have at least four things specifically configured, an IP address, the subnet mask for the local network, a primary gateway, and a name server.
DHCP is a client-server protocol that automates the configuration process of hosts on a network. With DHCP, a machine can query a DHCP server when the computer connects to the network and receive all the networking configurations in one go.
For a newly arriving host, the DHCP protocol is a four-step process.
-
DHCP server discovery
- The first task of a newly arriving host is to find a DHCP server to interact. This interaction is done using a DHCP discover message, which a client sends within a UDP packet to port 67.
- The UDP packet is encapsulated in an IP datagram.
- The DHCP client creates an IP datagram containing its DHCP discover message along with the broadcast destination IP address of 255.255.255.255 and a "this host" source IP address of 0.0.0.0.
- The DHCP client passes the IP datagram to the link layer, which then broadcasts this frame to all nodes attached to the subnet.
-
DHCP server offer(s)
- A DHCP server receiving a DHCP discover message responds to the client with a DHCP offer message that is broadcast to all nodes on the subnet, again using the IP broadcast address of 255.255.255.255.
- Each server offer message contains the transaction ID of the received discover message, the proposed IP address for the client, the network mask, and an IP address lease time—the amount of time for which the IP address will be valid. It is common for the server to set the lease time to several hours or days.
-
DHCP request
- The newly arriving client will choose from among one or more server offers and respond to its selected offer with a DHCP request message, echoing back the configuration parameters.
-
DHCP ACK
- The server responds to the DHCP request message with a DHCP ACK message, confirming the requested parameters.
Network Address Translation (NAT)
Network address translation takes one IP address and translates it into another. There are lots of reasons why we would want to do this. They range from security safeguards to preserving the limited amounts of available IPv4 space.
NAT is a technology that allows a gateway, usually a router or firewall, to rewrite the source IP of an outgoing IP datagram while retaining the original IP to rewrite it into the response.
NAT has become a popular and essential tool in conserving global address space in the face of IPv4 address exhaustion.
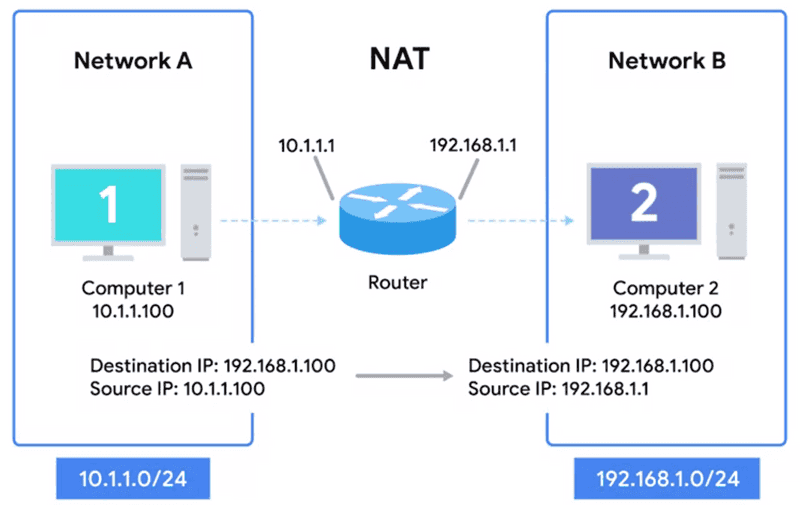
Let's say we have two networks:
-
Network A consists of the 10.1.1.0/24 address space, and Network B consists of the 192.168.1.0/24 address space.
-
Between these networks is a router with an interface on network A with an IP of 10.1.1.1 and an interface on network B of 192.168.1.1.
-
Computer 1 is on network A and has an IP of 10.1.1.100, and computer 2 is on network B and
has an IP of 192.168.1.100. Computer 1 wants to communicate with a web server on computer 2.
-
In this instance, the router is configured to perform NAT for any outbound packets.
-
Normally, a router will inspect the contents of an IP datagram, decrement the TTL by 1, re-calculate the checksum, and forward the rest of the data at the network layer without touching it. But with NAT, the router will also rewrite the source IP address, which becomes the router's IP on network B or 192.168.1.1. When the datagram gets to computer 2, it'll look like it originated from the router, not computer 1.
-
Now, computer two crafts its response and sends it back to the router. Knowing that this traffic is intended for computer 1, the router rewrites the destination IP field before forwarding it along.
-
NAT is hiding the IP of computer one from computer two, known as IP masquerading.
-
Using NAT like above, we could have hundreds of computers on network A, all of their IPs being translated by the router to its own. The entire address space of network A is protected and invisible to the outside world, known as one-to-many NAT.
Did you find this post helpful?
I would be grateful if you let me know by commenting below. Means a lot to me!
Sign up to get updates when I write something new. No spam ever.
Comments